How to Secure Integrations: Best Practices
Summarise the blog with AI

Your product depends on employee data moving reliably between systems. But every new integration adds a connection your team must secure, monitor, and maintain. With API traffic now making up over 71% of web activity, even small misconfigurations or expired credentials can lead to unauthorized access, compliance issues, or lost customer trust.
The solution lies in building a secure API integration approach from the start. Instead of treating security as a final step, you design integrations with strict authentication, encrypted data transfers, clear access controls, and continuous monitoring. This approach reduces risk and keeps employee data protected as it moves across platforms.
This guide explores how integrations work, the principles of integration security, and best practices for protecting sensitive data.
In a nutshell:
- Integrations connect multiple systems to automate data sharing, make workflows smoother, and keep data consistent across platforms, especially for HR and benefits software.
- Secure integrations rely on strong authentication, controlled access, data encryption, continuous monitoring, and compliance alignment to protect sensitive information.
- Best practices include applying least privilege access, monitoring activity, maintaining API versioning, implementing secure error handling, regular security testing, and clear data governance.
- Future trends focus on AI-driven threat detection, zero-trust models, API-first security, automated compliance, and platforms that simplify secure integrations.
What Are Secure Integrations, and Why Do They Matter?
API integrations allow different software systems to communicate and share data automatically. Most integrations today rely on APIs (Application Programming Interfaces). With APIs, you can request information or trigger actions from one platform to another.

For example, an HR system might send employee information to a payroll system through an API call. A benefits platform may pull eligibility data from HR software. An LMS platform may automatically sync employee rosters and job roles.
Here’s why it matters:
- System connectivity: Integrations connect different software systems so you can share data automatically. This removes the need for manual exports, spreadsheet uploads, or repeated data entry.
- API-based communication: Most integrations rely on APIs that allow your applications to request, send, and update information in real time between connected platforms.
- Technology stack compatibility: Integrations let your platform work with tools your customers already use, such as HRIS, payroll, and benefits systems.
- Workflow automation: Automated data syncing reduces repetitive tasks and helps keep employee data consistent across multiple platforms.
- Essential for HR platforms: HR Tech and benefits platforms depend on integrations for tasks like syncing employee rosters, managing payroll deductions, or updating lifecycle events.
- Operational efficiency: Without integrations, your team must manually transfer data between systems, increasing the risk of delays and data errors.
- Security considerations: Every integration creates a pathway for data movement. If your security measures are weak, these connections may expose sensitive employee data.
Also Read: What Is an Integration Partner? Explained
Core Principles Behind Secure Integrations
Secure integrations depend on a set of foundational security principles that protect your data throughout its lifecycle.
- Strong Authentication: Ensure every system connecting to your APIs proves its identity using secure methods like OAuth or token-based authentication. This prevents unauthorized services from accessing sensitive data.
- Controlled Authorization: After authentication, systems should only access the data they truly need. Limiting permissions reduces the risk of unnecessary exposure if an integration is compromised.
- Data Encryption: Encrypt all data moving between your systems using communication protocols like HTTPS. Encryption keeps sensitive information unreadable if intercepted during transmission.
- Least Privilege Access: Grant integrations only the minimum permissions required to perform their tasks. Restricting access helps prevent misuse of employee data and limits potential security damage.
- Continuous Monitoring and Logging: Track API activity and integration behavior through logs and monitoring tools. These systems let your team detect unusual activity quickly and respond promptly.
- Compliance Alignment: Secure integrations must follow regulatory requirements when handling sensitive data. Align your processes with standards like SOC 2 or HIPAA to maintain trust with your enterprise customers.
- Error Handling and Recovery: Design integrations to detect failures, retry requests, and notify your team when issues occur. Reliable recovery mechanisms keep data flowing securely and consistently.
These principles guide how integrations should be designed, implemented, and maintained over time.
8 Best Practices for Securing Integrations
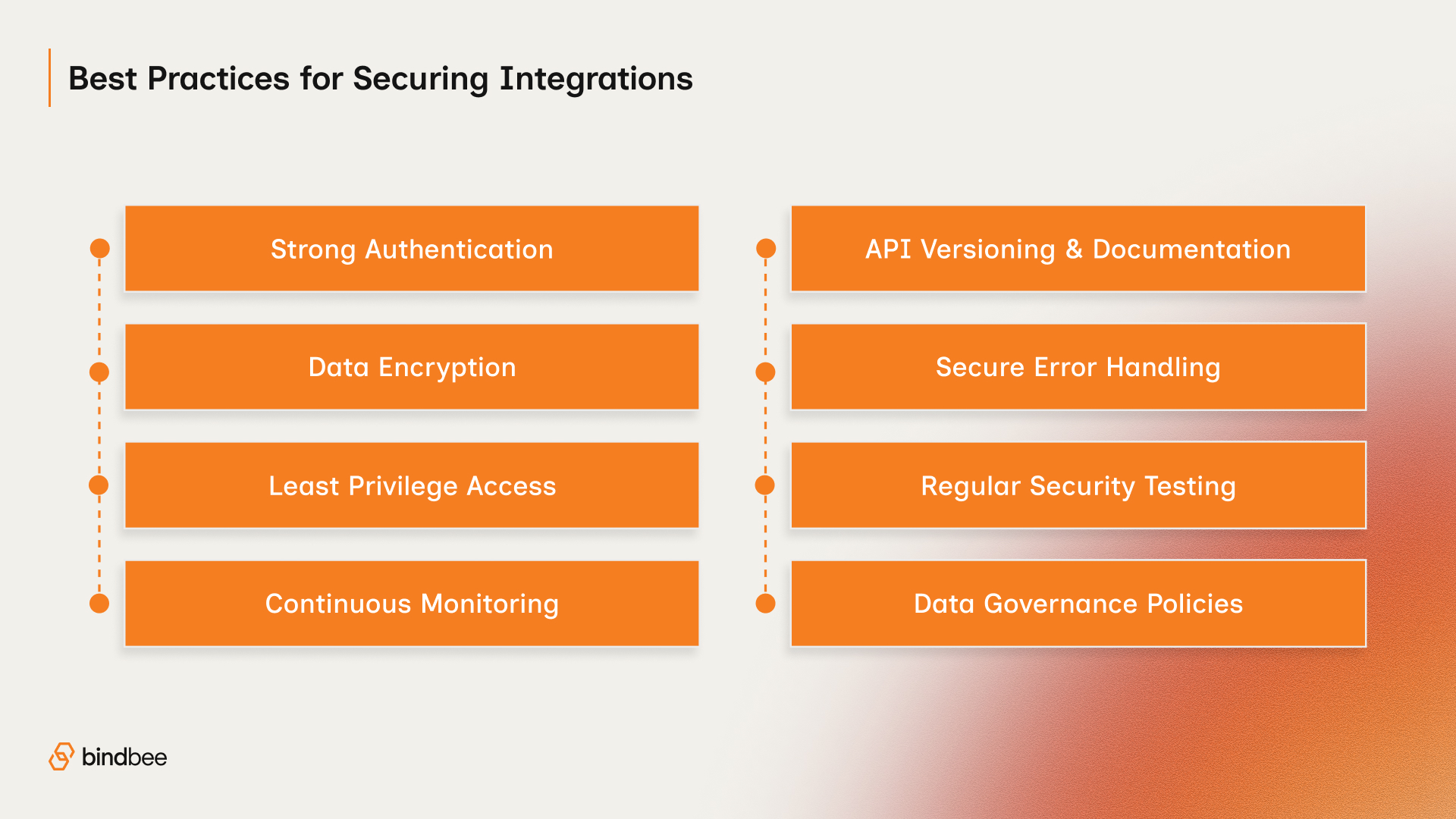
Security principles provide the foundation, but best practices translate those principles into actionable steps.
1. Use Strong Authentication Mechanisms
Authentication helps you make sure that only trusted systems and users can access your APIs. Weak authentication is one of the most common causes of integration breaches.
Strong authentication protocols help verify identity before any data exchange occurs.
Key practices include:
- Implement OAuth 2.0 or OpenID Connect instead of static API keys.
- Use short-lived access tokens to reduce exposure if credentials are compromised.
- Rotate credentials regularly to prevent long-term access risks.
- Enable multi-factor authentication (MFA) for administrative access.
Strong authentication prevents unauthorized systems from interacting with your APIs and forms the foundation of your secure integration strategy.
2. Encrypt Data During Transfer and Storage
Integrations constantly exchange sensitive data such as employee records, payroll details, and benefits eligibility information. Encryption helps you keep data protected even if it is intercepted.
Every integration should protect data both in transit and at rest.
Important encryption practices:
- Use TLS (Transport Layer Security) for all API communication.
- Encrypt sensitive fields in databases and storage systems.
- Secure backup systems and logs containing employee data.
- Avoid transmitting unencrypted credentials or tokens.
Encryption helps you keep data protected throughout its lifecycle, from the moment it leaves one system until it is securely stored in another.
3. Apply the Principle of Least Privilege
Many integration vulnerabilities occur because systems have more permissions than they actually need. The principle of least privilege limits access to only what is necessary.
By restricting permissions, you minimize damage if an integration becomes compromised.
How to implement this principle:
- Grant integration read-only access whenever possible.
- Restrict access to specific data objects rather than entire databases.
- Separate permissions for development, testing, and production environments.
- Conduct periodic permission audits to remove unnecessary access.
When your integrations operate with minimal permissions, attackers cannot easily escalate privileges or access unrelated systems.
4. Monitor Integration Activity Continuously
Your integrations run automatically and exchange large volumes of data. Without monitoring, you might miss errors or suspicious behavior.
Continuous monitoring helps your team identify issues early and respond before they escalate.
Monitoring systems should track:
- API request patterns and activity volume
- Failed authentication attempts
- Unexpected data access behavior
- Integration error rates or failures
Alert systems should notify your engineering team immediately when anomalies occur. This visibility helps you maintain system reliability while strengthening your secure integration posture.
5. Maintain API Versioning and Documentation
APIs evolve as vendors introduce updates, security patches, and new features. Without proper versioning, integrations may break or behave unpredictably.
Versioning helps you keep updates from disrupting existing integrations.
Effective API management includes:
- Maintaining versioned API endpoints for backward compatibility.
- Documenting authentication methods, data models, and security requirements.
- Deprecating outdated endpoints in a controlled manner.
- Communicating API updates clearly to development teams.
Clear documentation also helps your developers follow security best practices when building or maintaining integrations.
6. Implement Secure Error Handling
Errors are inevitable in complex integration environments. However, poorly designed error responses can expose system information that attackers may exploit.
Secure error handling protects sensitive system details while still providing your team with useful diagnostic information.
Best practices for error handling:
- Return generic error messages to external systems.
- Avoid exposing internal system architecture or database queries.
- Log detailed error information internally for troubleshooting.
- Implement retry mechanisms for temporary failures.
This approach helps your developers diagnose problems while preventing attackers from gathering valuable information.
7. Conduct Regular Security Testing
You should validate integration security continuously as your systems evolve. Regular testing helps you uncover vulnerabilities before attackers can exploit them.
Testing methods include:
- Penetration testing to simulate real-world attacks
- Automated vulnerability scanning for dependencies and APIs
- Security reviews during code deployment
- Integration stress testing to identify unexpected behavior
Regular testing helps you keep your integration architecture strong, even as systems grow more complex.
8. Establish Clear Data Governance Policies
Integration security goes beyond technical controls. Organizations also need clear policies governing how data is accessed, stored, and shared across systems.
Data governance provides accountability and helps you comply with industry regulations.
Key governance practices include:
- Defining clear data ownership responsibilities.
- Implementing audit trails for all data access events.
- Enforcing retention policies for sensitive employee data.
- Aligning practices with regulatory frameworks such as SOC 2 or HIPAA.
Strong governance helps you keep data protected throughout its lifecycle and across every connected system.
Also Read: Top 11 Application Integration Solutions to Watch in 2026
By implementing proven integration security practices, you can protect sensitive data and maintain system reliability.
Future Trends Shaping Secure Integrations

Integration security continues to evolve as software ecosystems become more interconnected. Emerging technologies and architectural shifts are changing how companies protect their integrations.
- AI-powered threat detection: Machine learning tools analyze API traffic patterns and quickly detect unusual behavior, such as abnormal data requests or suspicious access attempts, so your team can respond faster.
- Zero-trust integration models: Modern security frameworks require each system request to verify identity and permissions, ensuring that no connection is automatically trusted, even inside internal networks.
- Automated compliance monitoring: Security tools increasingly track integration activity in real time to ensure data handling aligns with standards like SOC 2 or HIPAA, making compliance audits easier.
- API-first security architecture: Organizations are building security controls directly into APIs, including authentication layers, access controls, and encrypted communication protocols.
- Integration platforms as security layers: Many companies now use integration platforms to standardize authentication, monitoring, and error handling, allowing your team to maintain a consistent, secure environment while reducing engineering complexity.
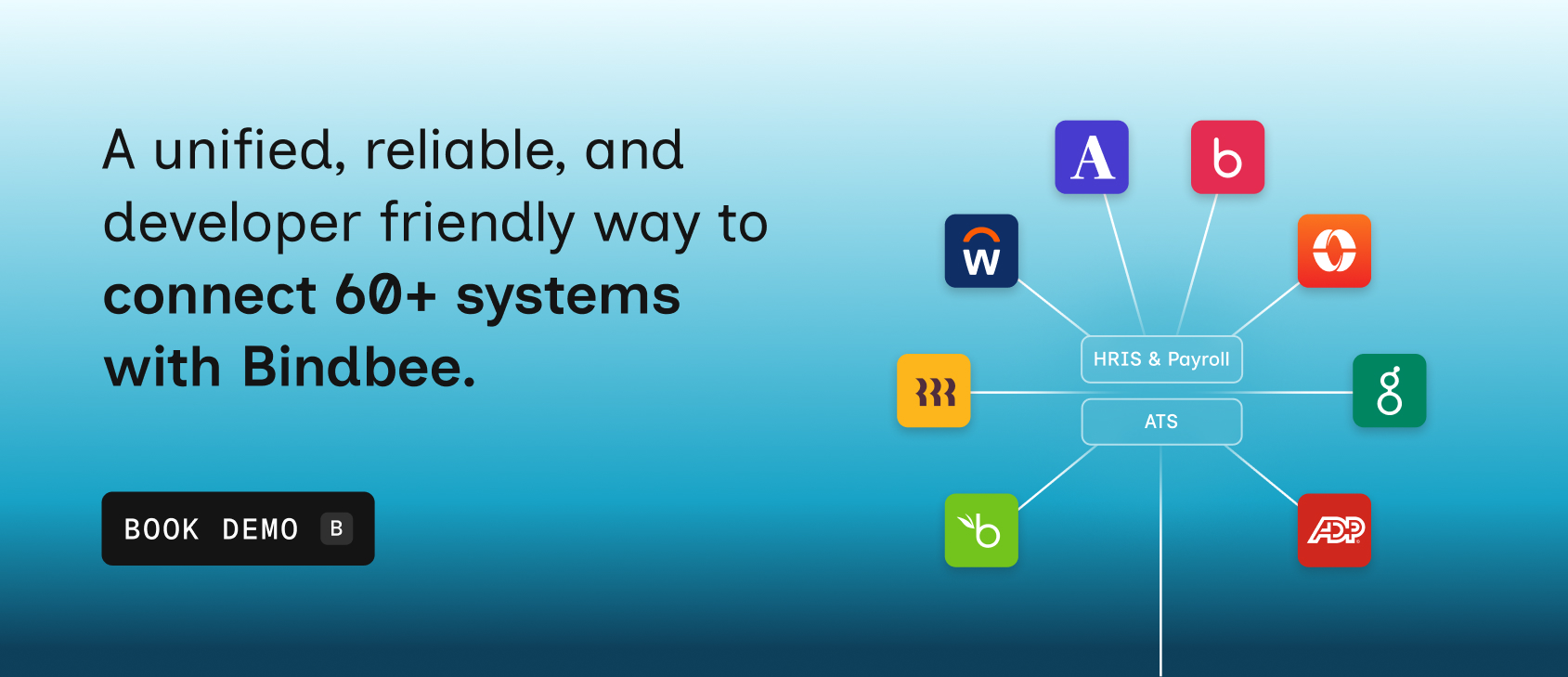
How Bindbee Helps You Build Secure HR Integrations
Maintaining a secure integration architecture becomes increasingly difficult as the number of integrations grows. Platforms like Bindbee simplify this process by providing prebuilt HR integrations with built-in security, monitoring, and standardized data models.
Here’s how we can assist you:
- Single API: Bindbee provides a unified API that connects your platform to more than 65+ HRIS, payroll, and benefits systems. Instead of managing separate integrations for each vendor, your team integrates once and gains access to all supported platforms.
- Standardized HR data models across systems: HR systems structure employee, payroll, and benefits data differently. Bindbee normalizes these datasets into consistent schemas so your product works with the same structure regardless of the underlying provider.
- Real-time syncing with webhooks and monitoring: Bindbee keeps employee and payroll data synchronized in real time using webhooks and automated sync processes. Monitoring tools track sync activity, detect errors, and ensure reliable data flows between systems.
- Enterprise-grade security and compliance: Security is built into the platform architecture with standards aligned to SOC 2, GDPR, HIPAA, and ISO 27001. Data is encrypted and handled through secure APIs designed for sensitive employment and payroll information.
- Faster customer onboarding and deployment: Employer connections can be established quickly using authorization flows that link HR systems in minutes rather than weeks. Faster onboarding reduces operational delays and helps platforms activate customers sooner.
- Reduced engineering maintenance overhead: Instead of dedicating engineering resources to building and maintaining integrations, your team relies on Bindbee’s infrastructure to manage vendor changes, schema differences, and API updates. This allows developers to focus on product innovation.
- Built for HR Tech, benefits, and retirement platforms: Bindbee’s unified API is designed specifically for companies that rely on employment data, such as HR Tech SaaS, employee benefits platforms, and retirement providers, ensuring integrations support real production workflows.
If your product relies on HR integrations, platforms like Bindbee provide a scalable path toward secure integration management.
Conclusion
Integrations play a critical role in modern software ecosystems. They allow platforms to exchange data automatically, streamline workflows, and deliver seamless experiences to users. However, every integration also introduces potential security risks if it is not designed and maintained carefully.
Organizations that rely on integrations must prioritize security from the start. Strong authentication, encryption, access control, and continuous monitoring help protect sensitive information while ensuring reliable data flows. These best practices create a foundation for building trustworthy and scalable software systems.
If your team wants to build reliable integrations without sacrificing security or engineering bandwidth, Bindbee can help. Book a demo to see how Bindbee can help your team build secure integrations faster and scale your platform with confidence.
FAQs
1. How can you implement strong authentication in integrations?
Use multi-factor authentication (MFA), OAuth 2.0, or API keys to verify identities. Ensure token expiration, rotation, and secure storage. Restrict access based on roles and permissions, and monitor authentication attempts to detect suspicious activity. Strong authentication reduces unauthorized access risks.
2. What steps ensure secure third-party integrations?
Vet vendors for security practices, use encrypted connections, and apply least-privilege access. Monitor data flows, maintain up-to-date software, and review API permissions regularly. Implement secure authentication, logging, and auditing to detect anomalies while keeping integrations compliant with internal and external standards.
3. How to handle input validation in integrations?
Validate all incoming data against strict formats, types, and length limits. Use whitelisting, escaping, and sanitization to prevent injection attacks. Reject unexpected or malformed inputs, and log validation failures. Consistent input validation ensures data integrity and mitigates security risks across integrated systems.
4. What compliance standards apply to secure integrations?
Standards depend on industry and data type. Common frameworks include GDPR, HIPAA, PCI DSS, and ISO 27001. Compliance ensures data privacy, secure storage, and proper handling across integrations. Following standards protects sensitive data and reduces legal and operational risks for interconnected systems.
5. How does penetration testing improve integration security?
Penetration testing simulates attacks on integrations to uncover vulnerabilities. It identifies weak authentication, misconfigured APIs, and insecure data handling. Addressing these findings strengthens defenses, ensures systems meet security standards, and reduces the likelihood of breaches or data leaks across integrated platforms.